Malware analysis Suspicious activity
4.7
$ 34.50
In stock
(566)
Product Description

The Role of Malware Analysis in Cybersecurity

1. General Flow of Signature-Based Malware Detection and Analysis

Using Python for Malware Analysis — A Beginners Guide, by Sarang S
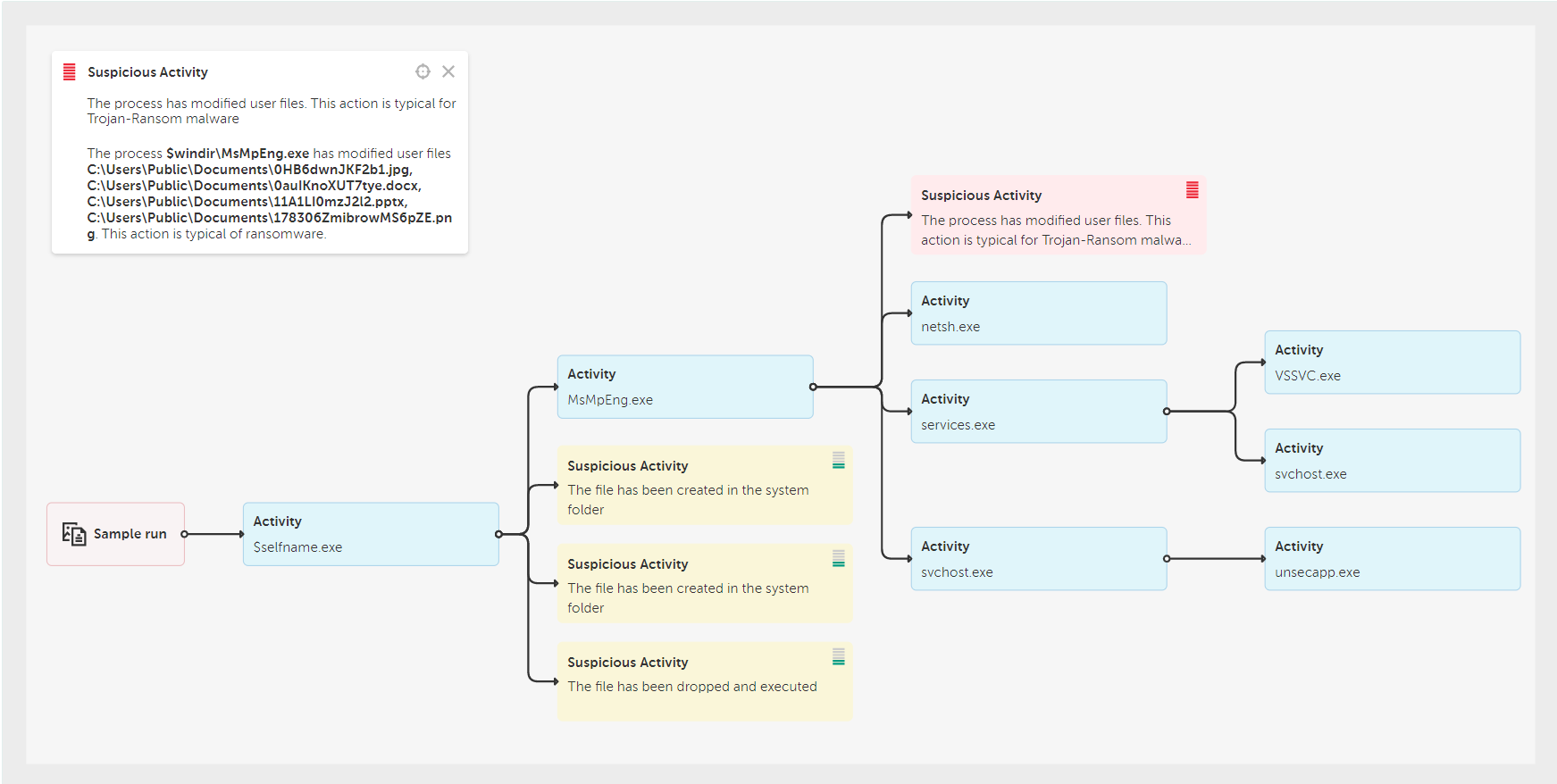
REvil ransomware attack against MSPs and its clients around the world
Suspicious Activity Details in Nebula – Malwarebytes Business Support
Highlight, take notes, and search in the book

Mastering Malware Analysis: A malware analyst's practical guide to combating malicious software, APT, cybercrime, and IoT attacks, 2nd Edition
ChatGPT-Powered Malware Analysis 2023
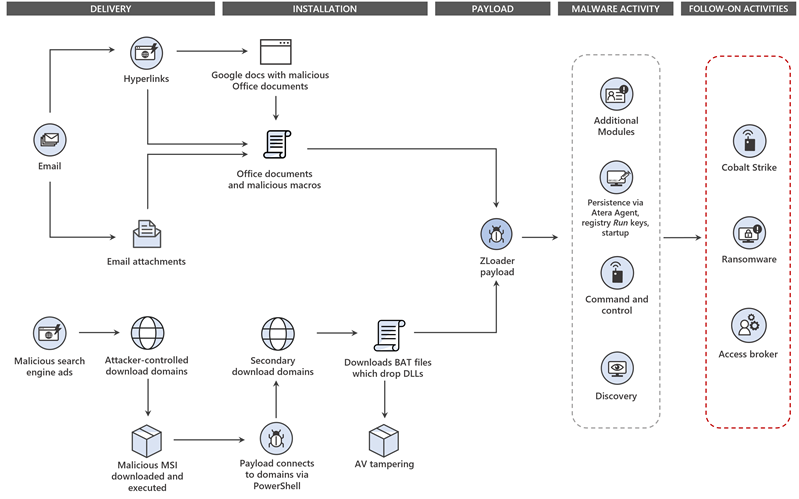
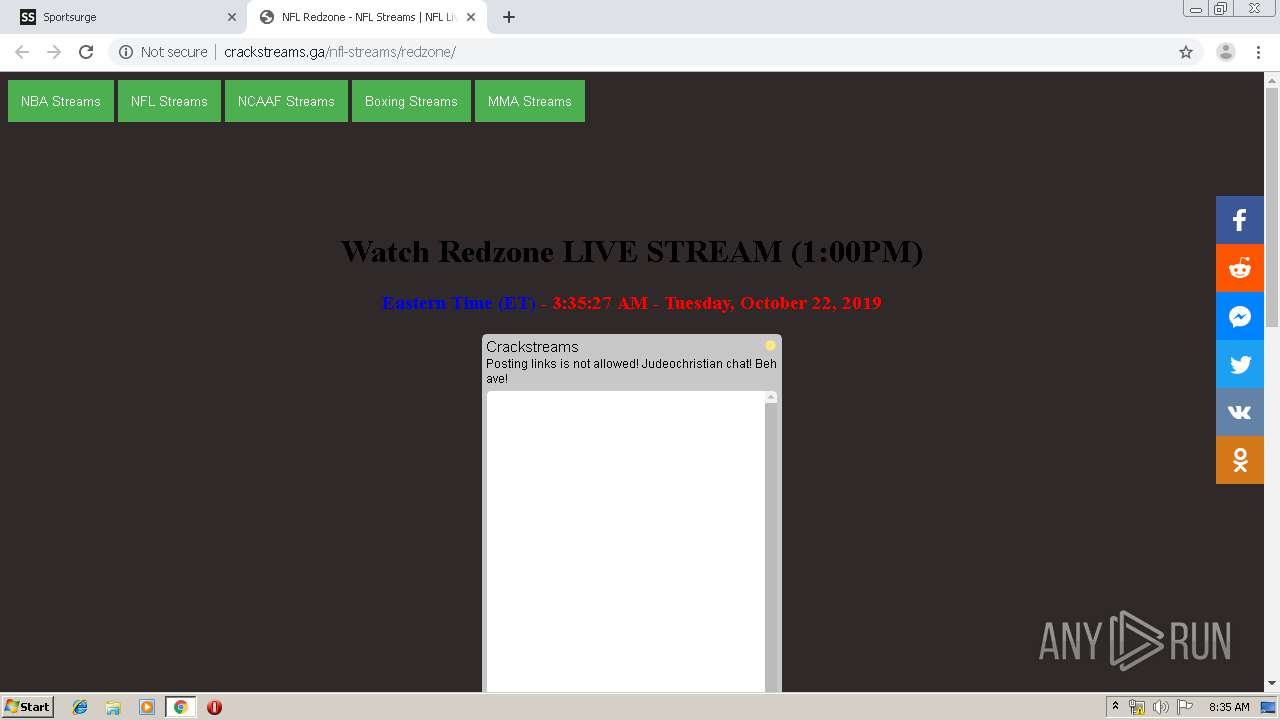
Dismantling ZLoader: How malicious ads led to disabled security tools and ransomware

IR - SOC174-124 - DogWalk 0-Day Activity

Malware Analysis Use Cases with ANY.RUN Sandbox - Security Investigation

Malware Analysis: Steps & Examples - CrowdStrike
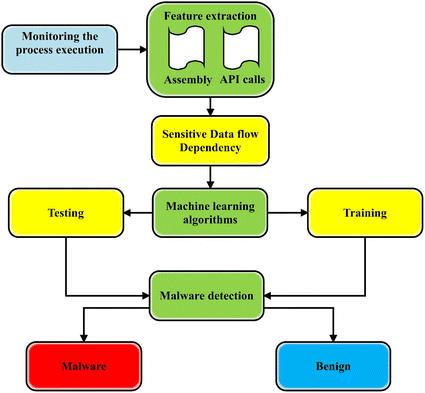
A state-of-the-art survey of malware detection approaches using data mining techniques, Human-centric Computing and Information Sciences

Windows Servers Security: How to Look for Suspicious Activities